Sessions vs JWT vs Cookies: Understanding Authentication Approaches
Learning web development in public. Writing simple, real-world explanations about web development concepts. Helping beginners understand why things work, not just how.
Authentication is something you’ll deal with in almost every backend project.
But the confusion usually starts here:
What are sessions?
What are cookies?
What is JWT?
And why do people argue about them so much?
Let’s break everything down step by step.
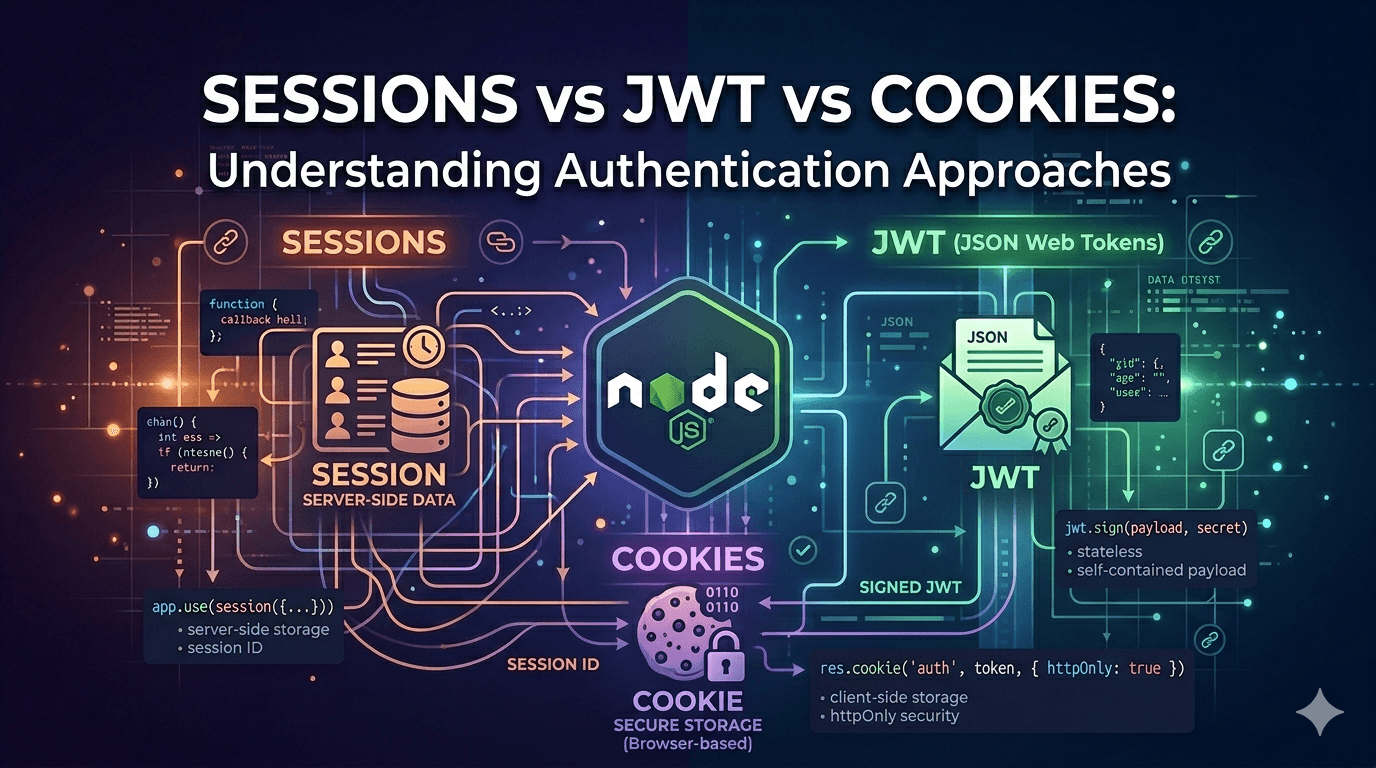
What Sessions Are
A session is a way for the server to remember a user.
When a user logs in:
Server creates a session (some data stored on server)
Server generates a unique session ID
Sends that session ID to the client (usually via cookies)
Now for every request:
Client sends session ID
Server looks it up
If found → user is authenticated
Example flow
User logs in → Server creates session → Session stored in DB/memory
→ Session ID sent to browser
Next request → Browser sends session ID → Server validates → Access granted
Key point
Data is stored on the server
Client only holds a reference (session ID)
What Cookies Are
A cookie is just a small piece of data stored in the browser.
That’s it.
Cookies are not authentication by themselves — they are just a storage mechanism.
What cookies can store:
Session IDs
JWT tokens
User preferences
Example
Set-Cookie: sessionId=abc123
Browser automatically sends cookies with every request to that domain.
Important
Cookies are used with both sessions and JWT.
What JWT Tokens Are
JWT stands for JSON Web Token.
It’s a self-contained token that carries user data.
Structure of JWT
header.payload.signature
Example:
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9
.eyJ1c2VySWQiOjEyMywicm9sZSI6InVzZXIifQ
.signature
What happens during login:
User logs in
Server generates JWT
Sends it to client
Client stores it (cookie/localStorage)
Client sends JWT in every request
Server verification
Server does NOT store anything.
It just verifies the token:
jwt.verify(token,SECRET_KEY);
If valid → user is authenticated
Key point
Data is stored inside the token
Server does not need to remember anything
Stateful vs Stateless Authentication
This is the core difference.
Stateful (Sessions)
Server stores user data
Needs memory/database
Every request depends on server state
Client → Session ID → Server → Lookup session → Response
Stateless (JWT)
Server stores nothing
Token contains everything
Each request is independent
Client → JWT → Server → Verify → Response
Differences: Session vs JWT
1. Storage
Session
- Stored on server
JWT
- Stored on client
2. Scalability
Session
- Harder to scale (needs shared session store like Redis)
JWT
- Easy to scale (no storage needed)
3. Security
Session
Safer by default
Server controls everything
JWT
Risky if token is leaked
Cannot be invalidated easily
4. Performance
Session
- Requires DB/memory lookup
JWT
- Faster (just verify token)
5. Logout Handling
Session
- Easy → delete session
JWT
- Hard → need blacklist or expiry
When to Use Each Method
Use Sessions when:
You want better security control
You are building traditional web apps
You need easy logout handling
You don’t care much about scaling yet
Use JWT when:
You are building APIs
You need scalability
You have multiple services (microservices)
You want stateless architecture
Use Cookies when:
You need automatic request sending
You are working with browsers
You want secure storage (HttpOnly, Secure flags)
Final Understanding
Cookies → storage mechanism
Sessions → stateful authentication (server-based)
JWT → stateless authentication (token-based)
If you remember just this, you’re already ahead of most beginners.
Simple Mental Model
Session = “Server remembers you”
JWT = “You carry your identity”
Cookie = “Browser stores stuff for you”